How Do Cybersecurity Strategies Benefit Businesses?
What is Cybersecurity?
Cybersecurity is the protection of internet-connected systems such as hardware, software, and data from cyber threats. Cybersecurity protects your critical systems and data from hackers who would steal your client’s sensitive information.
What is a Cybersecurity Strategy?
A cybersecurity strategy is a high-level, actionable plan for how your organization will secure its assets and sensitive information. Due to the changes in technology and cyber threats, this plan should be updated regularly to combat any threats.
How Do Cybersecurity Strategies Benefit Businesses?
Having an effective cybersecurity strategy can benefit your business in a multitude of ways. Not only does it help protect your business’s reputation with little to no breaches, but it also saves you from any potential revenue loss. Your business operations will continue to run smoothly and efficiently with no downtime due to hackers. Additionally, a cybersecurity strategy can benefit your employees by keeping them educated on proper cybersecurity procedures. This gives your company a competitive edge above other competitors.
Common Cyber Attacks on Businesses
Cyber attacks can often be so subtle you may not even realize you’ve been a victim until it is too late. Hackers are finding new ways to breach business networks every day, oftentimes including the following methods.
Malware — As generally malicious software, malware can include spyware, ransomware, viruses, and worms. Malware breaches a network through a detected vulnerability and can disrupt your business’s network infrastructure.
Phishing — A strange email from someone claiming to be your boss could actually be a virus hiding in plain sight. A phishing attack aims to steal sensitive data through something as harmless as an email.
Denial-of-Service — A denial-of-service attack floods a system or network with false traffic to exhaust resources or bandwidth, leaving you unable to respond to legitimate requests.
These are only a handful of the ways that hackers will attempt to steal sensitive information from your network. It’s key that your network is protected from these attacks and you properly assess how best to identify any weaknesses in your network.
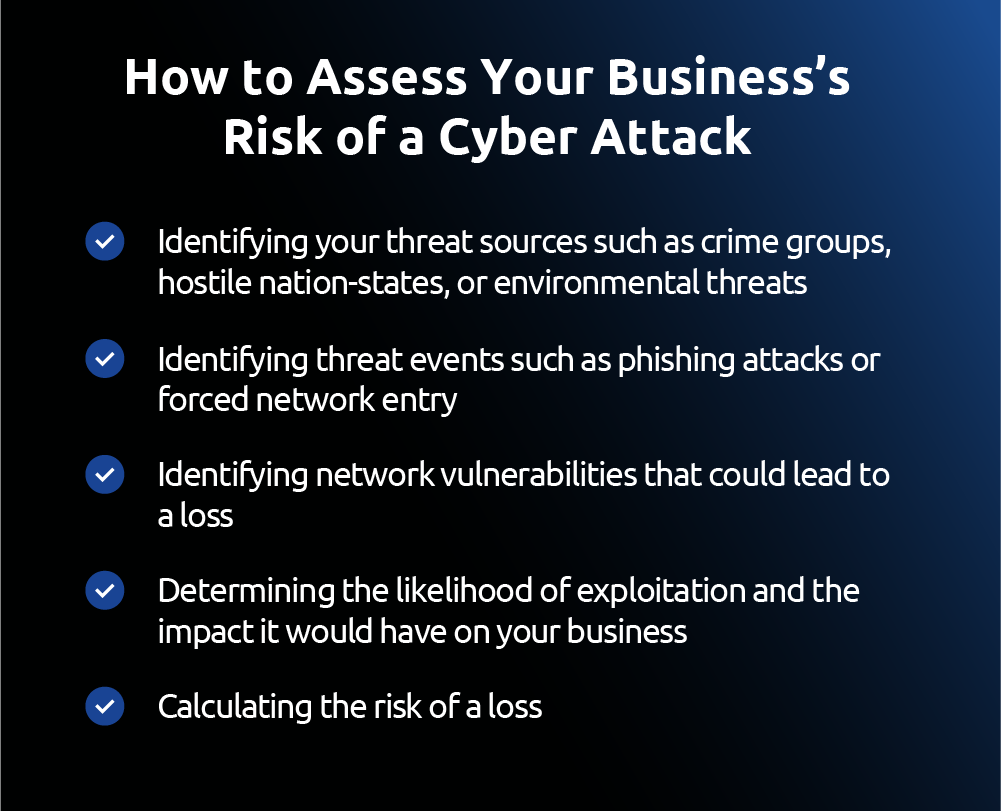
How to Assess Your Business’s Risk of a Cyber Attack
Assessing your business’s risk of a cyber attack is key in your steps of preventing one. Yet as the technology landscape continues to evolve, this assessment can prove to be difficult as threats continue to advance. Assessing your risk of a potential cybersecurity threat can include the following steps: Identifying your threat sources such as crime groups, hostile nation-states, or environmental threats Identifying threat events such as phishing attacks or forced network entry Identifying network vulnerabilities that could lead to a loss Determining the likelihood of exploitation and the impact it would have on your business Calculating the risk of a loss This painstaking process should be conducted thoroughly, or else your risk will not be properly assessed. Once you have discovered your vulnerabilities, it’s time to make a plan.
How Can Businesses Improve Their Cybersecurity?
Cyber Security Strategies for Small Businesses
When you are starting out small, hiring a large cybersecurity team may not be in the cards. However, this doesn’t mean that you can ignore the threat of hackers. A hacker targeting a small business can do significant damage to your business. There are many ways to protect your small business from a cyberattack.
Strategies include:
- Keeping your software updated
- Educating your employees to secure their security threats
- Moving your data to a secure cloud location
- Creating a response plan for when disaster strikes
- Staying secure in your business can be as simple as following these steps
Cyber Security Strategies for Enterprise Businesses
Enterprise businesses have much more financially to lose as you are carrying more high-security information. It is important that you build out your cyber security resilience to protect your critical assets.
Essential ways to protect your network include:
- Creating a password policy to help staff follow online security best practices
- Controlling access to critical data and systems
- Putting up a firewall to protect your internal network
- Using security software to continuously monitor your network for intrusion
What Should A Cybersecurity Strategy Include?
No matter what size your business is, your cybersecurity strategy should always include a line of defense against any hacker. Think of your business like a kingdom and the data like the treasure you are trying to protect inside. Your ideal cybersecurity should be enough protection so that you don’t fall victim to the enemy’s attacks. This includes:
- A next-generation security firewall to protect the perimeter of your network
- An intrusion protection system to monitor your network for malicious activity
- Computer protection such as anti-virus software and localized firewalls
These tools will help you protect your critical systems from a hacker finding a weakness in your network, as well as build up a solid best practice for your business.
Goals for Your Business’s Cybersecurity Strategy
Every time you log online, you are potentially putting your company at risk. Your cybersecurity plan should mitigate that risk and keep your assets securely protected. Additionally, your cybersecurity plan should identify what next steps are once you have been hacked to prepare for the worst.
Policies To Consider When Developing A Security Strategy
Developing a cybersecurity policy will give your company clear guidelines of what procedures to follow in case of an attack. It should be your roadmap of what to do when your network is breached, both from a security standpoint and an employee standpoint. A response plan is just as critical to have as a strong network protection plan. A cybersecurity policy must clearly spell out what each team and stakeholder has to do, say, and report during the event of a breach. It will look differently depending on your business and the risks you have. Your policy must also take into account any compliance issues you may have as well as industry risk.

Steps to Develop a Cybersecurity Strategy
Once you understand why your business needs a cybersecurity strategy, it’s time to take the steps into developing one. Your cybersecurity strategy should be the foundation of your approach to protecting your network and should be built out thoroughly with your business in mind.
Step 1. Conduct A Security Risk Assessment
This risk assessment will obtain all organizational data to assess, identify, and modify a business’s overall security.
Step 2. Set Your Security Goals
Establish the security details and goals that are necessary for your organization, and align them with the business goals for your company.
Step 3. Evaluate Your Technology
Once your sensitive assets have been identified, the next step is ensuring that your systems can properly secure them. If they can’t, it might be time to upgrade your products.
Step 4. Select A Security Framework
A security framework will provide guidance on the controls and systems needed to continuously monitor and measure the security of your organization. There are many out there to choose from, so be sure to keep your company’s unique goals in mind when you go looking for the right partner.
Step 5. Create A Risk Management Plan
A risk management plan is the most important part of a cybersecurity strategy. This plan will inform your employees on what to do in the event of a breach or loss of data.
Step 6. Implement and Continuously Evaluate Your Plan
Once you have created a plan, implement it and continuously evaluate its effectiveness on an ongoing basis, making changes when necessary.

How to Secure Your Networks
Once you create a strategic plan and put best practices in place, you need to make sure that your networks are totally secure at all times. Regularly performing a network audit, updating software, installing essential lines of defense such as VPNs and firewalls, and regularly conducting the proper system maintenance can keep your business aligned with its security at all times.

Your business deserves a telecommunications company that takes cybersecurity just as seriously as you do. As one of the only telecommunications companies on the island, we know how important network security is to protect your company’s data. Our experts at GTA have years of experience customizing individual cybersecurity networks for businesses. Reach out to our team today to learn more about how we can help you.
.png?width=795&height=795&name=GTA%20Pillar%20Page%20Designs%20V2-03%20(1).png)

